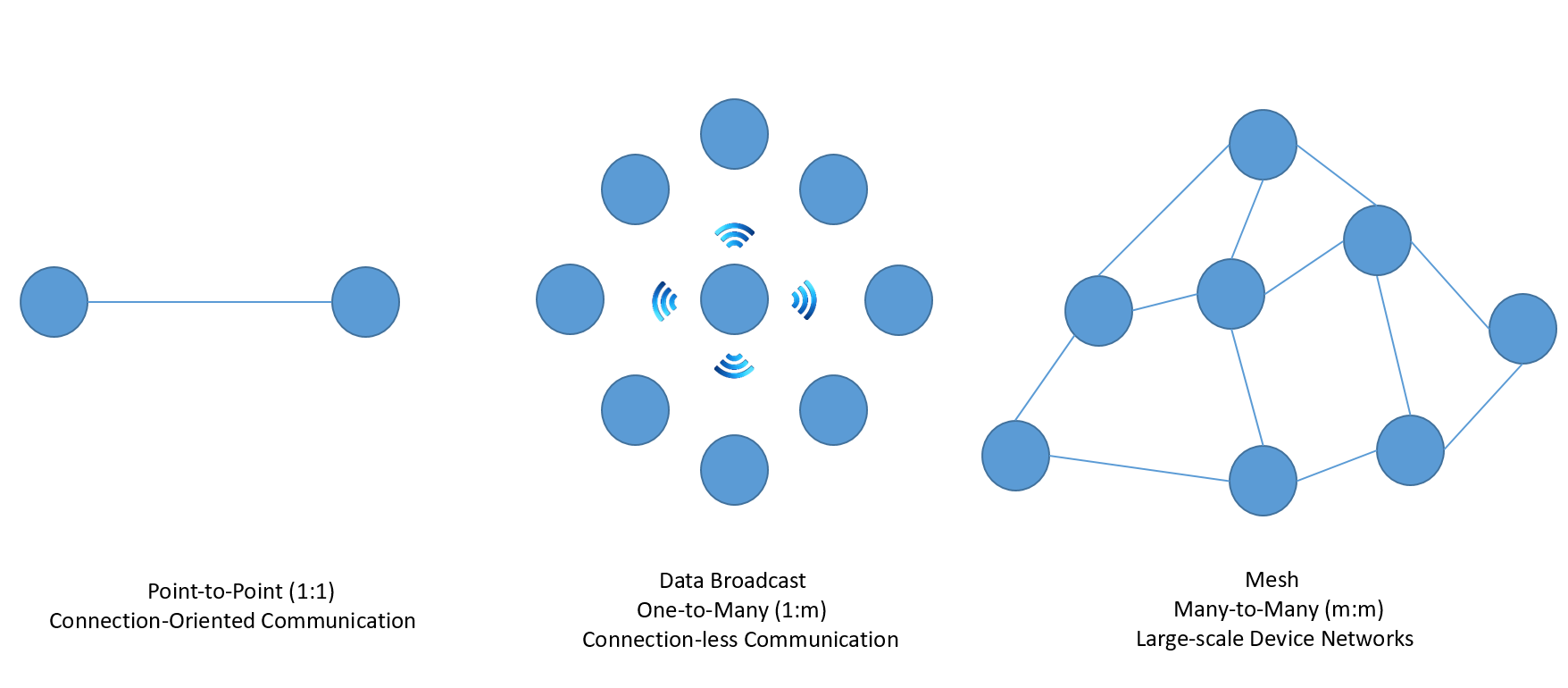
A BLE beacon broadcasting a signal to the nearby devices. Each device... | Download Scientific Diagram

Bleedingbit: Critical vulnerabilities in BLE chips expose millions of access points to attack - Help Net Security

Amazon.com: IoT Projects with Bluetooth Low Energy: Harness the power of connected things: 9781788399449: Bhargava, Madhur: Books

Amazon.com: BLE M3 Bluetooth Remote Shutter, Wireless Phone Camera Remote Control, Camera Shutter Remote Control with Bluetooth Wireless Technology, Create Amazing Photos and Selfies : Electronics